How to Be Anonymous Online? 7 Internet Anonymity Protection Tips Shared

When you realize you are living with strict internet censorship and surveillance, and want to acquire anonymity online, there are many ways you can go for this goal.
With the advent of the web, literally referring to the World Wide Web, people start to live in a hyper-connected world, with all things turned upside down and become easier and faster than ever before. Instead of paying much for a wire-powered phone call, a photograph, and a cinema movie, taking a really long time for a business journey, holiday travel, and news acquisition, and doing many more similar things in the last century, currently, we can effortlessly make all of that stuff happen immediately and still at low cost, only with the help of advanced Internet service and a smart device like a mobile phone or a laptop. Instant social chat, news world at the fingertip, one-tap photo-taking, streaming favorite films on the move, real-time virtual meetings, and live cams from around the world, examples are countless.
The Internet brings about great convenience indeed but delivers a higher chance of identity exposure and security risk at the same time. That’s why more and more people start to seek out ways to stay anonymous online. If you are one of those in demand, please keep on reading for 7 handy internet anonymity protection tips and tricks.

1. Use a Virtual Private Service to Be Anonymous to An Extreme
Virtual private network, commonly known as VPN, is the go-to tool to shield the web anonymity. With a VPN on your smart device, your IP address will be hidden totally and all of the traffic will be transmitted through an encrypted VPN tunnel and data safeguarded by first-class cryptography. As a result, none third-party, say ISP, government agency, and hacker, is able to track your real IP address, locate your physical place, collect your browsing history and personal information for further intentions. (Proxy server works alike, but considering there’s no data locking process, here it’s not listed in a single point.)
Here you can get PandaVPN – a slick and top online privacy and safety defender – to become anonymous right away.
Its 3000+ servers located in 73 countries worldwide help you mask and switch IP address to anywhere you prefer. Plus the most advanced ECC encryption and high-speed servers (with patented acceleration tech), you can enjoy a smooth and protected connection at will. Not only being anonymous, but also unlocking geo-restricted contents and speeding up online games in the meantime.
Available platforms: Windows, macOS, Android, iOS, Linux etc.
2. Use a More Private Browser like Tor
More often, we conduct daily web surfing with mainstream browsers like Chrome, Firefox, Safari, and Edge. When we want to be “invisible”, we take advantage of the embedded incognito mode or private windows to leave no history and cookies when quitting the browser. However, this type of behavior only belongs to private browsing, but not anonymous browsing, because even if there’s no trace left on the device afterwards, you are still tracked by the browser provider and many more.
Tor browser, on the contrary, works in a different way. As the flagship product of the Tor project which is devoted to aiding anonymous communication online, Tor browser anonymizes the users by routing all the traffic through its unique Tor network, specifically the multiple randomly chosen relay servers from volunteers around the world. This makes it the heaven for both the general public and offenders to do web usage secretly, including doing some illegal activities like drugs trafficking, gambling, arms trading, and pornography. Although there’re many outlaws accessing the dark web and committing crimes with Tor, it doesn’t mean police couldn’t follow the persons behind the screen up.
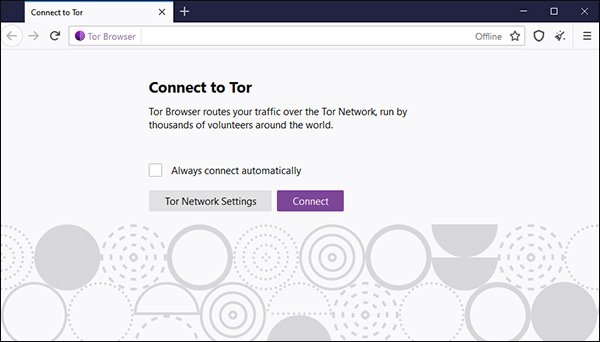
Tor browser is now available for Windows, macOS, Linux, and Android. And the obvious disadvantages are slow connection and browser extension incompatibility for flash etc.
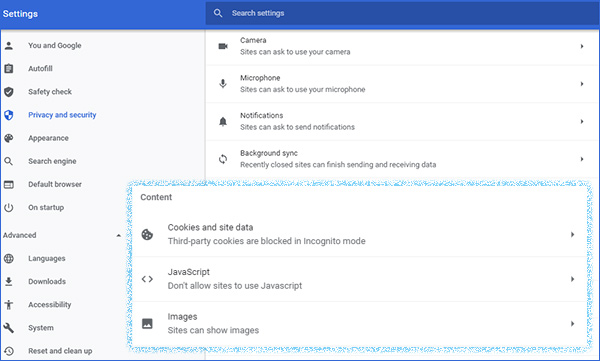
3. Stay Away from JavaScript, Cookies, Account Registration and Posting
How you are watched online inside the browser then? Setting aside the IP address, cookies, JavaScript, account log-in, public social share, and posting are the main approaches for big brothers to trace you easily. Therefore, don’t allow any site to run JavaScript and turn off cookies under the privacy and security settings of browsers, and take precautions before any open privacy disclosure on Facebook, Twitter, LinkedIn, Instagram, etc. to prevent the happening of cyber manhunt.
4. Use Other Encrypted or Anonymous Services Besides Browser
The Tor browser mentioned above is actually one part of a known free open source Tor project, which still has some other implements like instant messaging program – Tor Messenger (discontinued) and TorChat, file sharing tool OnionShare, Vuze BitTorrent client and so on. Absolutely, browsers are just a typical medium of our online activity.
Beyond that, we also work frequently with search engines, messaging apps, email services, cloud storage, web shopping sites, forums, communities and such. Here are some common suggestions for various service types: If you are dealing with important files, talking about politically sensitive topics, and similar, you’d better get a portable secure system like TAILS, access more privacy-focused search engine like DuckDuckGo, employ encrypted or anonymous informing applications like Signal, secure anonymous email with ProtoMail, leverage anonymous cryptocurrency payment like Bitcoin…
Related Reading: Is Online Shopping Safe? 10 Tips to Shop Online Safely >
5. Don’t Click Spam Links and Permit App to Access Your Device
Spammers scatter all over the internet, from the average web page to email, social chat to free files/services. Keeping your email address far away from them is crucial to hide your virtual identity.
We’ve come up with taking care of account registration earlier. What’s more, another conventional identity leakage of yourself is to allow the software, web services to access your device, such as the storage, the webcam, the contact, the microphone etc. No matter what it is, once you open the door for them to access, you won’t have the basic privacy any more, not to mention anonymity.
6. Apply 3rd Ad-blocking and Anti-tracking Helper
Your digital footprint may be the tracing target for various parts, among which advertisers should be the #1 for monetary purposes. Sometimes, you may surprisingly come across an expected advertising picture or video on the sidebar of a page. Is that just a coincidence? Surely not, because it’s just an outcome of your online behaviors being collected and analyzed by the advertiser. According to your certain search act or browsing list, the advertising agency just picks you as the potential buyers of their product.
To avoid web tracking, there are dedicated anti-ads and -tracking tools nearby, be it browser plugin or standalone software like AdGuard and Disconnect. You can choose either to enhance the security experience. If you don’t want to build so many different tools, you are free to pick a feature-packed VPN with an ad-blocker function preloaded here.
Most of the programs, especially the mobile apps, will ask for acceptance on its terms and condition, and still the permission to access location, storage and other device information. Do check out the rules carefully and allow what you can accept, deny what you are not willing to, or even quite the usage of the app with unfair terms.
7. Other Things Together
As the successor and the encrypted version of HTTP, HTTPS is now a better guarantee of security. You can still make use of virtual machines to access the web without trace. Moreover, many tech geeks don’t advocate using voice assistants for smart home…
Quite a lot of people ask how to watch Snapchat and Instagram stories anonymously. Strictly speaking, this is much easier to achieve because there are many free viewing and downloading services. If there’s no third-party tool, borrow an account or sign up a new one to present as another passerby.
Verdict
How to remain anonymous when surfing the internet? To stay away from tracking and personal information collection, you’re suggested to sign out of services, keep silent on the web, utilize anonymous browsers like Tor and VPN software to enhance privacy.
 Vic Knott
Vic Knott  2021.12.26
2021.12.26