What Is Dark Web? 6 Things You May Want to Know
Get a deep dive into the dark web so that you won’t take it as a place only for evil and be afraid to talk about it.
Not all netizens know clearly about the dark web, which makes them wonder what is dark web, how does dark web work, what’s dark web used for, how to visit it, as well as is this kind of thing legal, secure, or not. Now without further ado, let’s just jump right in these questions one by one in detail, unlocking the mystery of the Dark Web.

1. Definition of Dark Web
Dark Web, aka Dark Net, simply put, is a series of network content that can be accessed only with special browser app (specifically Tor browser or I2P) and settings. In other words, common browsers like Chrome, Firefox, Safari and Microsoft Edge are unable to reach and view the dark web resources and the search engines like Google, Bing and DuckDuckGo unable to crawl, index and display related search results still.
Estimates place the size of the deep web at between 96% and 99% of the internet. Only a tiny portion of the internet is accessible through a standard web browser—generally known as the “clear web”.
2. Dark Web vs. Deep Web, What’s the Difference?
Generally, the web or say World Wide Web Dark web, consists of two-part – surface web and deep web, the former of which is what search engine can find and we can use everyday while the latter one is invisible to common people. You may say that it seems deep web and dark web are the same thing, but that’s not the truth.

The dark web is a part of the deep web because the deep web refers to all websites that are hidden from search engines, intentionally or accidentally, legal or illegal, whereas the dark web only concludes the sites that’re concealed by the web owners deliberately. Why do they make the pages invisible to the general public? Most probably, it lies in the illegality or sensibility nature of the page content. Hence it’s not weird for common people to take the dark web as cyber heaven of criminal activity.
To help you better understand the difference between the deep web and dark web, please check out some examples here.
| Name | Examples |
| Deep web | The content of all private thing on the web like email box, social media profile, web banking, streaming, gaming accounts, private forums, private networks, data stored on private database, medical/financial records, academic information, various legal/scientific/research/governmental reports & documents & papers etc. |
| Dark web | Illegal websites, TOR-encrypted sites (e.g. freenet/I2P/Riffle), Silk road, Red room, Alphabay, Hansa, Dream, drug trafficking, political protest, etc. |
What percentage of the internet is the dark web? According to the data online, deep web accounts for over 90% (some even say about 96-98%) of the whole Internet while dark web only about 0.01%.
3. How to Access the Dark Web? How Do Dark Web + Tor Work?
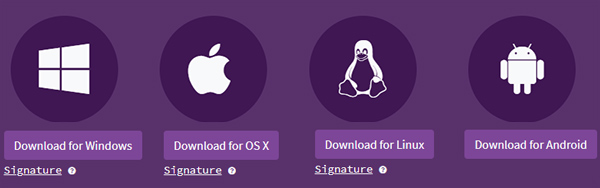
To access any dark web site, you have to equip your device with above mentioned browser called Tor – currently the only web browser featuring complete anonymous browsing. Now let’s move on to the steps one by one.
Step 1 – Free download Tor from its official site and finish the installation.
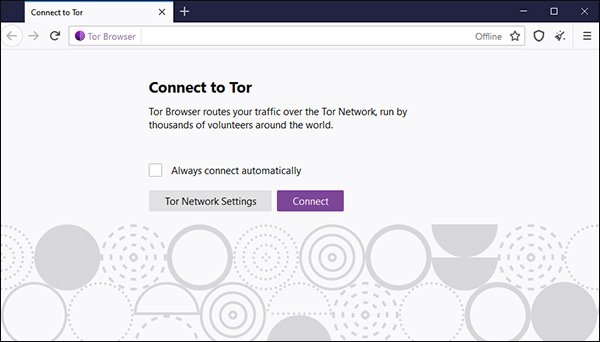
Step 2 – Start the Tor browser after setup. For the first time, you are requested to click the “Connect” button to have the Tor connection work. You can tick the “Always connect automatically” to avoid manual connection in the future.
Step 3 – Input the special URL address for dark web that ends with .onion, e.g http://6nhmgdpnyoljh5uzr5kwlatx2u3diou4ldeommfxjz3wkhalzgjqxzqd.onion/index.htm (the address of The Hidden Wiki, a dark web directory), and then enter to make the connection happen.
Step 4 – When it’s successfully connected, you can browse the web as normal. If the address is invalid or the connection gets a failure, you will need to check the link or go on to another one.
Besides browsing medium browser and site link type, it seems that there’s nothing special. However, below the surface, the workflow of using Tor to visit the dark web is quite different from common network activities.
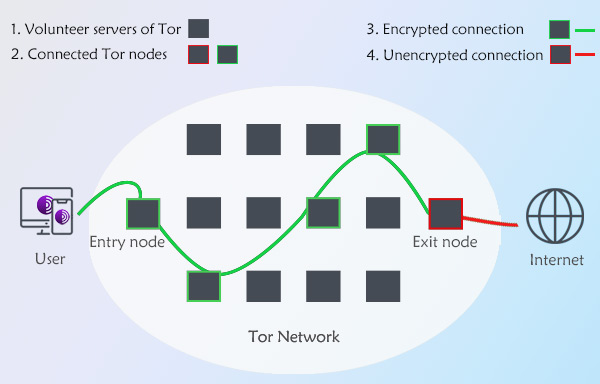
Firstly, the traffic within Tor is not sent to the target website server directly but routed to many middle-server and then the final destination over Tor Network. It is a volunteer network and has over 6,000 relays. By randomly picking multiple Tor relays to encrypt and transport traffic and data, Tor network does keep everything private and everyone involved anonymous on the web so that nobody would track and monitor him or her, knowing the real location, browsing histories, and personal information. This multi-node mechanism is also the root reason why Tor keeps anonymity better than other private browsers meanwhile Tor help the dark web provide shelter for illegal acts.
4. What Is Dark Web Used for?
It is true that the dark web is used for criminal activities only? Before you dig out the answer for your curiosity, let’s have an overview on the top Tor onion service (onion service was called hidden service until the renaming in 2015)
| List Name | Content |
| Top onion service types | 1. Drugs | 2. Market | 3. Fraud | 4. Bitcoin | 5. Mail 6. Wiki | 7. Whistleblower | 8. Counterfeit | 9. Forum |10. Anonymity |
| Top crimes taking place on dark web | 1. Drug Trafficking | 2. Child Pornography 2. Illegal Financial Transactions | 4. Information Breach and Theft 5. Human Trafficking | 6. Arms Trafficking 7. Murder and Contract Killer | 8. Terrorism 9. Hacking and other web attack |10. ransom |
Extreme online privacy must give rise to criminal behaviors. We have to admit that compared to regular clear/surface web, dark web is an ideal place for committing network crimes for its high level of anonymity. So quite a lot of people use it completely for legitimate reasons to do “wrong things” mentioned above or not.
But still a portion of users just take it for legal private communications, viewing geo-blocked content or simply satisfying their curiosities of the unearthly dark web. Except for the 100% original dark web sites, many internet service providers have launched the dark web or say Tor versions of their services, like Facebook and BBC, to help the users worldwide bypass local internet censorship and acquire information or services freely. In addition, Tor works with common web sites, which means you are enabled to surf the surface web with better privacy easily.
In short, the purpose to utilize the dark web comes down to a user’s actual identity and demand, and all possible intentions can be found here, be it a journalist for guarding the essential materials, a protestor holding up the sign, a drug dealer selling the heroin, card fraudsters trading the stolen credit card, a heavily-censored resident unblocking region-restricted web service, etc.
5. Is (Accessing) Dark Web Legal and Secure to Enter Into?
Generally, either the dark web itself or the manner of accessing dark web is theoretically not illegal. Similar to the legality of (using) a VPN, what makes it illegal is what happens and you do on the dark web, surely it also varies from territories. If you are in a freer place like the US and UK, only when you do law-prohibited things on the dark web like pornography and illegal drug distribution will you be the target of the Internet police. If you live in a nation with less net freedom like China, Russia, and Iran, maybe only visiting the dark web for gaining some objective news is illegal.
As to whether it’s safe to access the dark web content via Tor, after knowing how Tor works in the earlier paragraphs, it’s easy to draw that it’s relatively much safer than common web browsing thanks to the multi-relay encrypted data transport.
6. You’ll Be Shielded Better amid the Dark Web Journey, with Tor Plus VPN
Considering those who stepping into the dark web must want to have the highest possible privacy to avoid being tracked or hacked during the process, anyone who’s ready to access the dark web is suggested to equip the device with an extra VPN program.
VPN and Tor are two different things. Since they both have their own different encryption methods – Tor has decentralized layer of independent nodes and VPN has VPN protocol and VPN encryption, forming them into a team means delivering users a dual protection, especially when you are connecting to a public (Wi-Fi) network.
Here PandaVPN is a stellar virtual private network tool you can run over Tor before navigating to the dark web. It’s not only compatible with Tor-available platforms like Windows, macOS, Android, and Linux, but also has iOS version to protect all network actions on these system-based smart machines.
Set aside browsing the dark web, equipping your mobile, PC and even smart TV with a VPN will give you benefits too when streaming HD/4K media content, uploading/downloading (P2P torrent) file, playing online games, chatting on the web, and doing many other things. All in all, no matter your goal is to mask real location, achieve online privacy, bypass content filter of any cause, remove bandwidth throttling, or secure your online shopping, you can trust this quality VPN service.

A word of caution anyway after you’ve finished this “what is dark web” post: since the dark web is foreboding to some degree just as it sounds like, you should take your care when setting your foot in this brand new Internet field.
 Vic Knott
Vic Knott  2021.11.29
2021.11.29